Fake Airdrop Scams: Types and Red Flags To Avoid
Fake airdrops are one of the fastest-growing attack vectors in crypto. Here's how to claim real ones without getting your wallet drained.

- Crypto airdrop scams in 2025 have reached record-breaking levels, with fraud and impersonation scams driving total crypto crime losses to $17 billion .
- Fake airdrop campaigns grew by 1,400% year-over-year, using AI-driven tactics and phishing-as-a-service
- Always use a burner wallet with minimal funds when claiming, never your main holdings wallet
- Check what permissions a site is requesting before you sign anything, and run from any "claim" page that asks for your private key or seed phrase
What Is a Crypto Airdrop?

A crypto airdrop is a highly anticipated crypto event when a Web3 project distributes free tokens to wallet addresses, usually to reward early users, build community, or decentralize token ownership.
Uniswap’s legendary 400 UNI airdrop in 2020 turned early users into overnight earners, and Hyperliquid distributed over $7.5 billion in tokens to its community in late 2024, the largest airdrop in crypto history.
The biggest 2025 crypto airdrops by peak value were led by Story Protocol at about $1.4 billion, Berachain at about $1.17 billion, Jupiter at about $791 million, Animecoin at about $711 million, and Linea at about $437 million.
So airdrops are good right? Well, apart from sybil attacks and points farming, there are other bigger issues, all to do with those dreaded airdrop scams.
What are Fake Airdrop Scams?

Fake crypto airdrops are one of the oldest tricks in the book, and they still work. Scammers pose as real projects offering free tokens, then funnel victims to phishing sites, fake social giveaways, or malicious NFTs.
Connect your wallet to claim your “reward” and you might be signing a transaction that empties it entirely. Others go simpler: pay a small gas fee upfront, never see it again. Some just want your seed phrase. The attack method varies, but the outcome rarely does. Your crypto ends up in someone else’s wallet.
Why Do Crypto Users Fall for Airdrop Scams?

Airdrops require you to connect your wallet to a website and sign a transaction.
That’s the exact same workflow a crypto wallet drainer uses to steal your funds. Scammers know that the promise of free tokens lowers skepticism and increases urgency.
As Kerberus documented in its psychology of crypto scams research, reward anticipation makes people overlook warning signs they’d normally catch.
“The Web3 ecosystem sets users up to fail. Social engineering drives the majority of real losses because we expect people to identify threats they have no way to detect. Users face these attacks during distracted moments or high-stress situations when cognitive capacity fails..”
Alex Katz, Kerberus CEO
The result? Fake airdrops have become one of the most profitable attack vectors in Web3 security. According to Chainalysis, crypto scam losses hit an estimated $17 billion in 2025, with impersonation attacks growing 1,400% year-over-year. A big chunk of those losses came from users who thought they were claiming legitimate tokens.
7 Deadly Airdrop Scam Types in Q2 2026
Fake airdrops aren’t a single trick. They’ve branched into several distinct attack patterns, each refined to exploit different user behaviors. Here are the types showing up most frequently right now.
- AI-powered social engineered airdrop scams

The fastest-growing category. According to Chainalysis, AI-enabled scam operations generated 4.5x more revenue than traditional scams in 2025, and impersonation attacks grew 1,400% year-over-year. Scammers now use deepfake videos of project founders, AI-generated customer support agents, and highly personalized phishing messages to promote fake airdrops.
In March 2026, a phishing campaign targeting OpenClaw developers on GitHub promised $5,000 in fake CLAW tokens, using targeted social engineering that referenced users’ actual GitHub activity to appear legitimate.
The cloned site loaded obfuscated JavaScript designed to drain wallets the moment someone connected.
- Cloned claim sites with wallet drainers
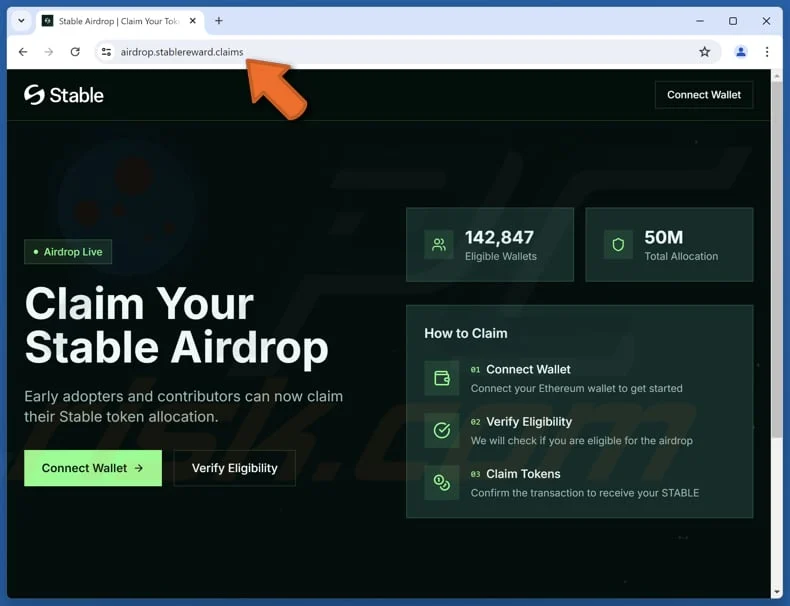
Source: PCRisk
This is the most common and most damaging type. Scammers create pixel-perfect copies of a legitimate project’s website, add a “Claim Airdrop” or “Connect Wallet” button, and promote it through fake X accounts, Discord DMs, or even Google search ads. When you connect and sign the transaction, you’re not claiming tokens.
You’re granting a malicious approval that lets a wallet drainer empty your holdings. In 2024 and 2025, cloned sites targeting projects like HEX, Wall Street Pepe, and Sui all used this method, with the HEX clone activating a drainer the moment a wallet was linked. A study reported that wallet drainer attacks alone stole $494 million from 332,000 addresses in 2024.
- Poisoned token drops
Instead of luring you to a site, scammers send unsolicited tokens directly to your wallet. The token name or metadata contains a URL. When you investigate it, try to sell it on a DEX, or visit the linked site, you’re funneled into a drainer contract. In June 2025, the FBI issued a public service announcement specifically warning about this tactic on the Hedera network, where scammers were airdropping NFTs with malicious “memo” URLs into non-custodial wallets.
- Hacked account impersonation
Source: PCRisk
When scammers compromise a verified X account, a project Discord admin, or even a founder’s profile, the fake airdrop announcement suddenly has real credibility behind it.
In 2023, hackers took over Vitalik Buterin’s X account and promoted a fake NFT airdrop that stole $700,000 from victims. The SEC’s own X account was hacked in January 2024 and used to post a link to a crypto wallet drainer disguised as an airdrop claim page. If a trusted account can be compromised, any account can be.
- Drainer-as-a-service kits
The scariest part of the current airdrop scam wave is how accessible it’s become. Drainer-as-a-service platforms like Inferno Drainer (which stole over $80 million before being shut down) and Pink Drainer ($75 million+) sold turnkey phishing kits on Telegram.
Affiliates with zero technical knowledge could spin up a convincing fake airdrop scam page, deploy it, and split profits with the kit operators. Even after some of these services shut down, the model persists, and copycat services continue to emerge.
- Delayed drain attacks
This one catches even careful users off guard. You sign a malicious approval during what seems like a harmless airdrop claim, but the attacker doesn’t drain your wallet immediately. They wait days, weeks, or even months until your balance grows, then execute the drain.
In August 2025, one user lost $908,551 in USDC from an approval they had signed 458 days earlier. The scammer had been monitoring the wallet the entire time, waiting for the right moment. This is why revoking approvals after every claim interaction is non-negotiable.
Read our new guide on how to remove token approvals in Q2 2026!

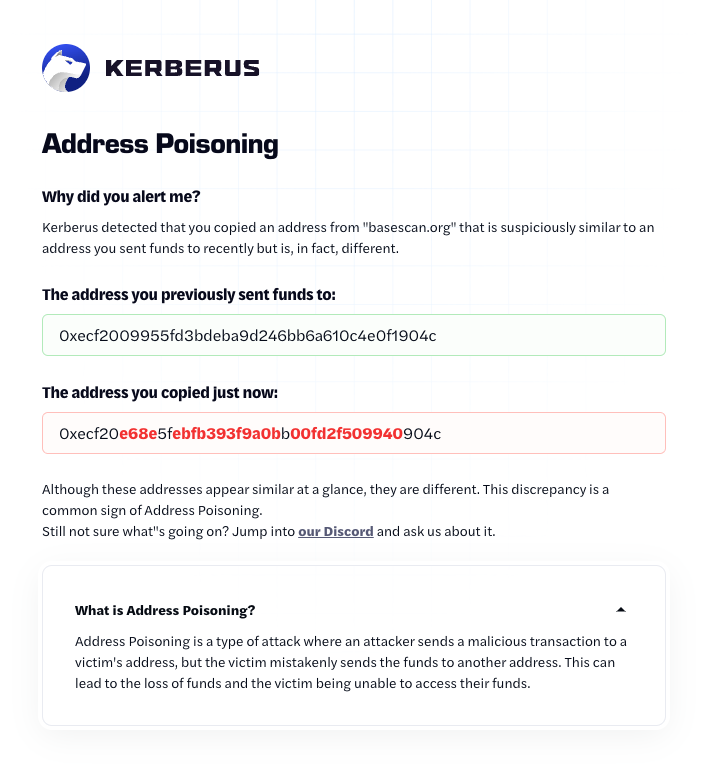
- Dusting attacks and address poisoning
A dusting attack happens when scammers send worthless, scam tokens directly to your wallet. The goal is to get you to check them on a block explorer, which contains a link to a phishing site, or try to move them, which can drain your wallet.
Address Poisoning: Scammers send a tiny amount of tokens from an address that looks almost identical to one in your transaction history, hoping you will copy-paste their address for future transactions. One unlucky user lost $50 million recently in the lottery of all attacks.
Biggest Red Flags of a Fake Airdrop or Scam
Before you connect your Web3 wallet to any claim page, check for these warning signs. If even one of them shows up, walk away.

1. No official announcement on verified channels

Legitimate airdrops are announced through the project’s official website, verified X account, and Discord or Telegram channels. If you heard about it through a DM, a reply thread, or a random Telegram group, and you can’t find it mentioned on the project’s actual homepage, it’s almost certainly a web3 phishing attempt. Scammers now use AI to create convincing fake project accounts that look nearly identical to the real thing, so always cross-reference multiple official sources.
2. It asks for your seed phrase or private key
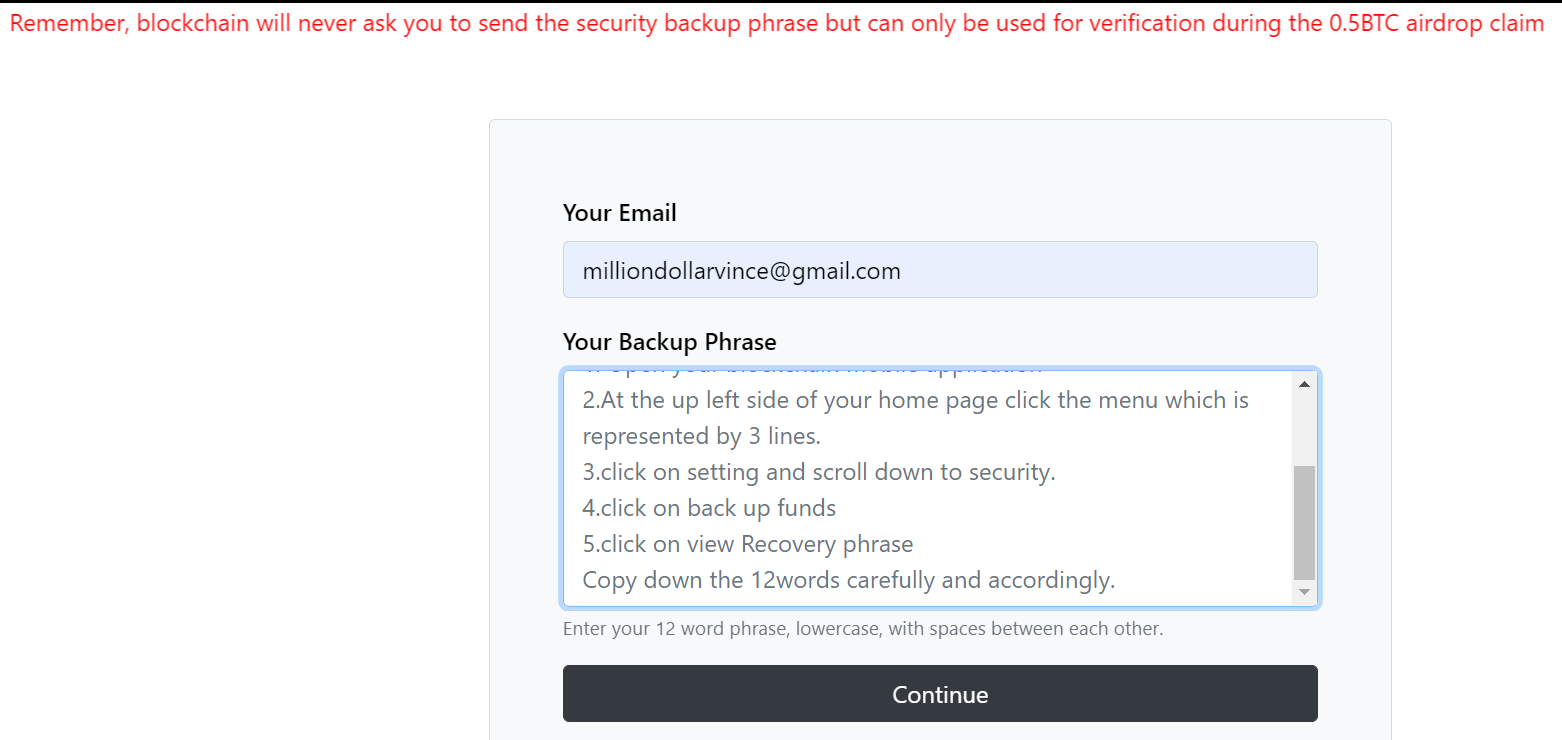
Source: Stackexchange
This should be an instant dealbreaker, every time. No legitimate project, airdrop, or platform will ever ask for your seed phrase or private key. Not to “verify” your wallet, not to “unlock” your tokens, not for any reason at all. If a page asks for these, you’re looking at a scam site built to steal everything in your wallet.
3. It requires an upfront payment or “gas deposit”
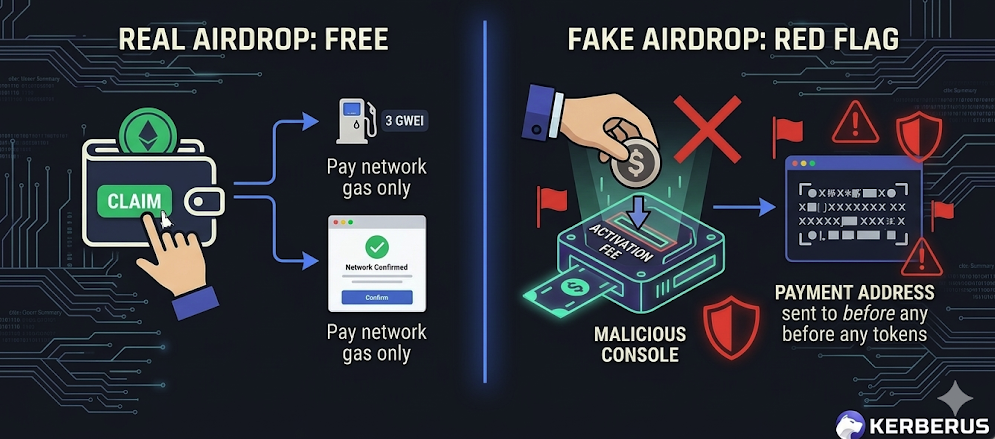
Real airdrops are free. You might pay standard network gas fees when claiming, but you should never send crypto to a specific address or pay an upfront “activation fee” to receive tokens.
This is a classic web3 social engineering tactic that exploits the fact that gas fees are a normal part of crypto transactions.
If they want your money before giving you money, that’s not an airdrop.
4. Unrealistic reward amounts
“Claim $5,000 in free tokens instantly!” Does it sound too good? It is.
Legitimate airdrops vary wildly in value and are usually tied to specific on-chain activity or holding criteria. Massive guaranteed payouts with zero effort are bait, designed to trigger FOMO and override your judgment.
As covered in Kerberus’s Web3 Security Threats 2026 guide, fake airdrops are specifically designed to exploit reward anticipation.
5. Unsolicited tokens appearing in your wallet
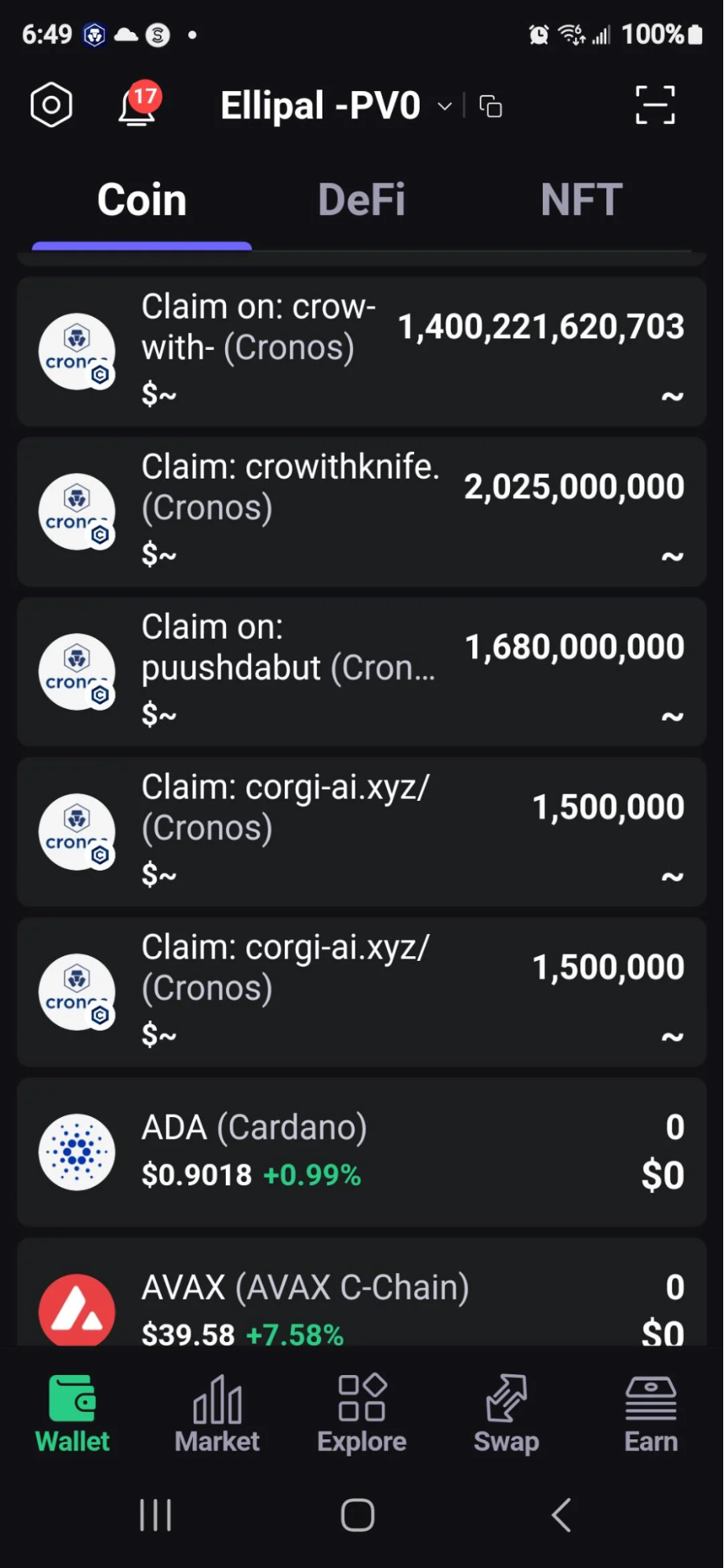
Source: Reddit
Sometimes scammers skip the landing page entirely and just airdrop worthless tokens straight into your wallet. When you try to interact with them, sell them, or visit the token’s website, you end up on a malicious claim portal that drains your real assets.
This is a honeypot setup. The rule is simple: never interact with tokens you didn’t expect to receive.
How to Use a Burner Wallet for Airdrops in 5 Steps

This is the single most important safety practice for anyone claiming airdrops, and most guides barely mention it.
A burner wallet is a separate non-custodial wallet you create specifically for interacting with claim pages and new dApps. It holds only a small amount of crypto for gas fees, nothing else. If the site turns out to be malicious, the worst case scenario is losing a few dollars in gas, not your entire portfolio.
Here’s how to set one up in 5 easy steps:
- Create a new wallet in MetaMask, Phantom, or your preferred wallet app like Trust Wallet or Solflare. Use a fresh seed phrase, completely separate from your main wallet
- Fund it with just enough native tokens (ETH, SOL, etc.) to cover gas fees for the claim transaction
- Connect only this wallet to airdrop claim sites
- After claiming, verify the received tokens are legitimate using a block explorer and token contract checker before transferring anything to your main wallet
- Revoke any token approvals you granted after you’re done. Tools like revoke.cash let you review and revoke permissions
Think of it like self-custody best practices applied to airdrop farming. Your main wallet should never touch a claim page directly.
What to Check Before You Connect Your Wallet
Even with a burner wallet, you should verify a few things before signing any transaction on a claim site. Most wallet drainer attacks rely on you blindly approving a transaction without reading what it actually does.
Verify the URL.
Bookmark the project’s official site and access it directly. Scammers register lookalike domains with tiny character swaps (kerberus.com vs. kerberuss.com, for example) or use Cyrillic characters that look identical to Latin ones.
Never click claim links.
Whether they’re from X replies, Discord DMs, or Telegram messages, even if they appear to come from official accounts. DON’T TOUCH THEM. .
Read the transaction before you sign.
When a site asks you to sign a transaction, your wallet will show you what permissions you’re granting. Watch specifically for setApprovalForAll requests or unlimited token spending approvals. These are the exact permissions wallet drainers abuse. A legitimate airdrop claim should request a simple token transfer, not broad approval over your entire wallet. If a site is requesting a malicious approval that grants it access to assets beyond what you’re claiming, reject and disconnect immediately.
Use a transaction simulator like Kerberus.

Tools that preview what a transaction will do before you confirm it are one of the best defenses against drainer scams. If the simulation shows tokens leaving your wallet instead of entering it, you’ve just caught a drainer in the act.
Kerberus Sentinel3’s transaction scanning and the acquired Pocket Universe simulation tool are built for exactly this.
How Kerberus Blocks Fake Airdrop Sites
Fake airdrops are a core threat that Kerberus Sentinel3 is built to stop. Where most Web3 security tools rely on static blocklists, Sentinel3 uses AI-powered detection that identifies malicious sites in real time, often before they’ve been reported by anyone.
When you navigate to a fake airdrop page, Sentinel3 blocks the site before your wallet can connect to it. No connection means no malicious approval, no drained assets. The extension also flags fake accounts on your X feed through its Social Shield feature, cutting off one of the primary channels scammers use to distribute phishing links.
Behind the scenes, Active Protection monitors your wallet addresses across chains, watching for signs of address poisoning and other on-chain attacks. And if a smart contract vulnerability or suspicious approval somehow slips through, Sentinel3’s transaction scanning catches it at the signing stage.
The numbers back it up: a 99.9% detection rate across 1000+ EVM chains and Solana, zero user losses since January 2023, and up to $30,000 in coverage per transaction through the Fairside partnership. You can install Sentinel3 here in seconds.
FAQ
Can You Get Scammed Just by Connecting Your Wallet to an Airdrop Site?
Yes. Connecting your wallet to a malicious site and approving a transaction can grant the attacker permission to withdraw your tokens. The risk isn’t in the connection itself, but in the approvals you sign afterward. This is exactly how drainer-as-a-service kits like Inferno Drainer operated, stealing over $80 million through fake airdrop phishing pages.
How Do You Know if an Airdrop Is Legit?
Check the project’s official website and verified social channels for an announcement. Cross-reference on aggregators like CoinGecko or CoinMarketCap. Look for a transparent team, a credible community, and a history of development activity. If you can’t find the airdrop mentioned in any official source, don’t touch it.
What Should You Do if You Already Connected to a Suspicious Airdrop?
Immediately revoke any token approvals you granted using revoke.cash or a similar permission manager. Transfer your remaining assets to a new wallet with a fresh seed phrase. Review your recent transaction history on a block explorer for any unauthorized transfers. If you use Sentinel3, Active Protection will also monitor for follow-up attacks on your address.
Are Hardware Wallets Safe for Claiming Airdrops?
Hardware wallets protect your private keys from being extracted, but they do not protect against malicious approvals you sign on the device itself. If you approve a drainer transaction on your hardware wallet, your funds are just as vulnerable. Always use a burner wallet for claims, regardless of wallet type.
About Kerberus

Kerberus is a trusted Web3 cybersecurity company protecting users across 1000+ chains with real-time scam detection and MEV defense. Its team has led and advised security work across top crypto ecosystems since 2023, with zero losses and 99.99% safety for its 250,000 users. It also offers up to $30,000 in coverage on user funds.
Kerberus Sentinel3 is a real-time Web3 security engine which users can install as a browser extension in seconds. It helps users stay safe by automatically detecting phishing, wallet drainers, and social engineering threats across chains, helping crypto users identify and block scam attempts before irreversible losses occur.
Related reading:
Written by:
Werner Vermaak is a Web3 author and crypto journalist with a strong interest in cybersecurity, DeFi, and emerging blockchain infrastructure. With more than eight years of industry experience creating over 1000 educational articles for leading Web3 teams, he produces clear, accurate, and actionable organic material for crypto users.
- •8+ years in crypto & blockchain journalism
- •1000+ educational articles for leading Web3 teams
- •Former content lead at CoinMarketCap, Bybit, OKX
Related Guides
See more guides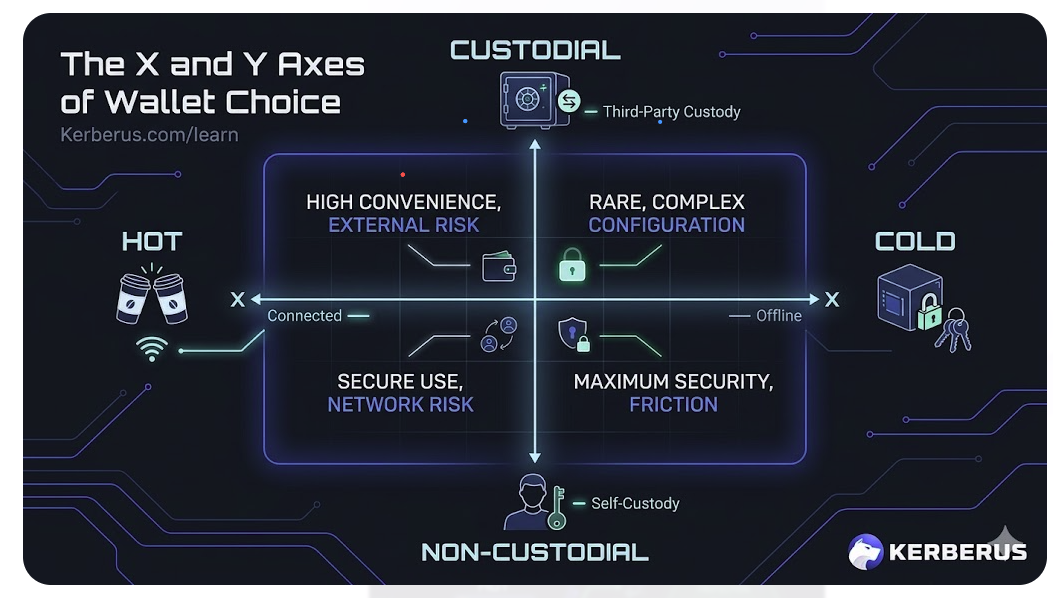
Crypto Wallets For Beginners: Your Need-To-Know Guide
Apr 11, 2026 • 4 minutes read

How to Revoke Crypto Token Approvals in 2026
Mar 28, 2026 • 4 minutes read

How to Read a Crypto Transaction Before You Sign It
Mar 23, 2026 • 4 minutes read
Bitcoin 101 For Beginners: BTC’s Past, Present and Future
Mar 19, 2026 • 4 minutes read
Install once & immediately get protected from scams, phishing and hacks. Zero losses for 250k+ users in 3 years. Now with up to $30,000 in coverage.
