Crypto Wallets For Beginners: Your Need-To-Know Guide
Hot or cold, custodial or self-custody, the wallet you pick determines how safe your crypto actually is. Here's how to make the right call in 2026.
- Your crypto wallet does not store your crypto. It stores the private key that proves you can move it. Lose the key, lose everything.
- Custodial wallets (exchanges) are fine for small, active holdings. They are not a sensible long-term home for significant funds.
- The most secure setup for most users is a split: a non-custodial hot wallet for daily use, a hardware wallet for long-term storage, and a real-time security layer like Kerberus Sentinel3 covering the gap between the two.
Most people pick their first crypto wallet the same way they pick a cereal at the supermarket: they grab whatever’s at eye level, whatever the person next to them recommended, or whatever came bundled with the exchange they signed up on. Convenience, not security, makes the call.
That bias has consequences. In the first half of 2025 alone, wallet compromises accounted for roughly $1.71 billion in stolen funds across just 34 incidents, making it the single largest category of crypto loss for the period. The overwhelming majority of those losses were preventable. The people who lost funds were not unusually careless. They just made wallet decisions without fully understanding what they were deciding.
Picking the right crypto wallet is one of the most consequential choices you’ll make in Web3. This guide breaks down every major wallet type, where each one falls short, and how to build a setup that actually fits how you use crypto.
What a crypto wallet actually does (and doesn’t do)
Before picking a wallet, it helps to clear up the most common misconception in crypto.
A crypto wallet does not hold your cryptocurrency. Your assets live on the blockchain, always. What the wallet holds is your private key, the cryptographic proof that you are authorised to move those assets. Think of it less like a bank account and more like a set of credentials. The wallet is the keychain, not the vault.
Lose the private key, or the seed phrase derived from it, and you lose access to every asset tied to it. Hand it to someone else, deliberately or through a phishing attack, and they have full control of your funds from that moment on.
Every wallet also generates a corresponding public key, which works like a bank account number. Share it freely. The private key is the opposite: it should never be shared with anyone, for any reason, ever.
Should I Choose A Hot, Cold, Custodial or Self-Custody Wallet?
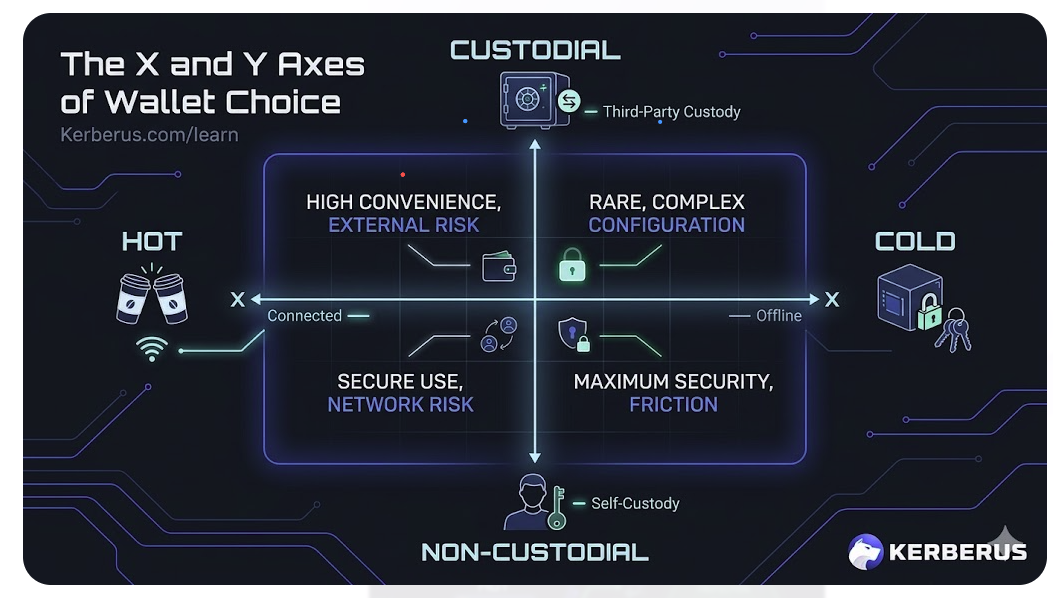
Every crypto wallet sits somewhere along two dimensions, let’s call them X and Y. Getting both right matters more than any specific brand recommendation.
These two axes combine into four configurations. Most real-world wallets fall clearly into one of them.
| Wallet type | Keys held by | Internet connected | Example |
|---|---|---|---|
| Custodial hot | Exchange | Yes | Binance, Coinbase |
| Non-custodial hot | You | Yes | MetaMask, Phantom |
| Non-custodial cold | You | No | Ledger, Trezor |
| Non-custodial multisig | Distributed | Optional | Safe (Gnosis) |
Hot vs cold wallets
- Hot wallets are connected to the internet.
- Cold wallets are not.
That internet connection is exactly what makes hot wallets convenient for daily use, and exactly what makes them more exposed to remote attacks. Cold wallets remove that exposure by keeping your keys offline at all times, but they add friction every time you want to transact.
There are buttons to push, on-device confirmations to complete, cables to plug in, software and firmware updates to run. It’s another device that you maybe didn’t cater for.
For many users, that friction feels like a bug.
For your security, well, it’s actually the feature.
Custodial vs non-custodial wallets
With a custodial wallet, a third party, usually an exchange like Binance or Coinbase, holds your private keys on your behalf. You access your funds through a login, like online banking, and trust that the platform will give you access whenever you need it.
With a non-custodial wallet, also called self-custody, you hold the keys yourself. No intermediary. No middleman. Full control, full responsibility. Full risk.
Should I Still Use Custodial Wallets in 2026?

When you buy crypto on an exchange and leave it there, you are using a custodial wallet. The exchange generates and manages your private keys. You access your funds through a login, just like online banking.
The main appeal here is familiarity. There is no seed phrase to manage, no risk of losing access because you misplaced a piece of paper, and customer support exists if something goes wrong. For anyone new to crypto, this lowers the barrier to entry considerably.
The trade-off is counterparty risk. You’re using a “trusted intermediary” to transact with a digital asset on a network designed to be completely trustless, with no need for middlemen. All in the name of convenience.
In crypto, convenience kills.
Just like a bank, if your exchange collapses, your crypto goes Kaboom. Like I experienced with Cryptopia in 2020 and FTX in 2022.
When an exchange holds your keys, you are trusting that it remains solvent, secure, and willing to give you access to your funds whenever you want them. FTX demonstrated what happens when that trust is unearned and quickly misplaced: Billions in customer funds became inaccessible overnight.
Exchanges can also restrict withdrawals, freeze accounts under regulatory pressure, or suffer hacks that affect customer balances directly.
The old saying in crypto cuts to the heart of it: not your keys, not your coins.
What they’re good for (and not)
Repeat this after me.
- Custodial wallets are reasonable for small amounts you plan to trade actively, or for users who are just getting started and are not yet comfortable managing their own security.
- They are not a sensible long-term home for significant holdings.
Still don’t believe me.
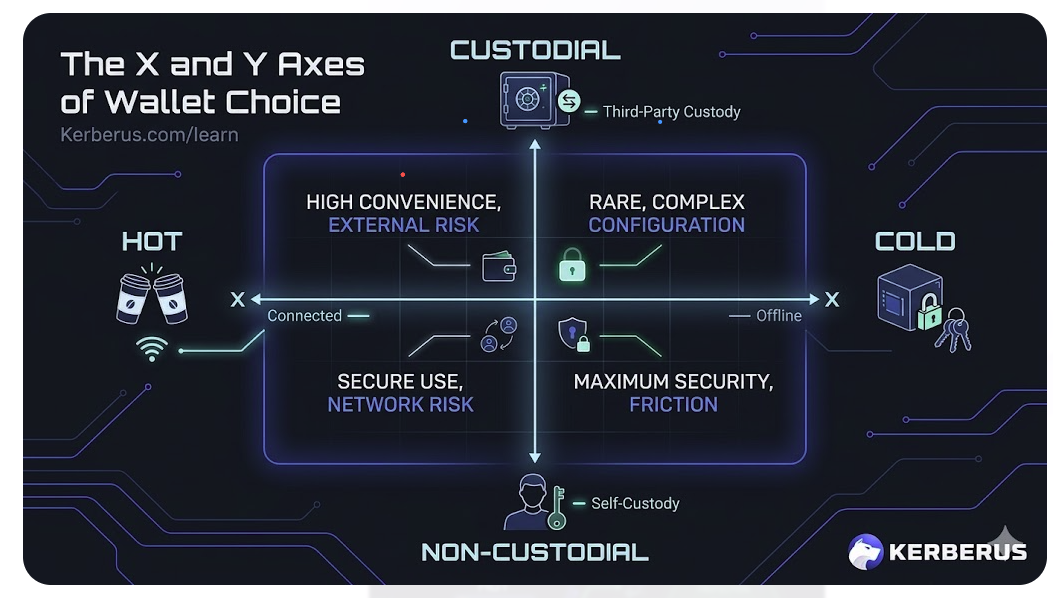
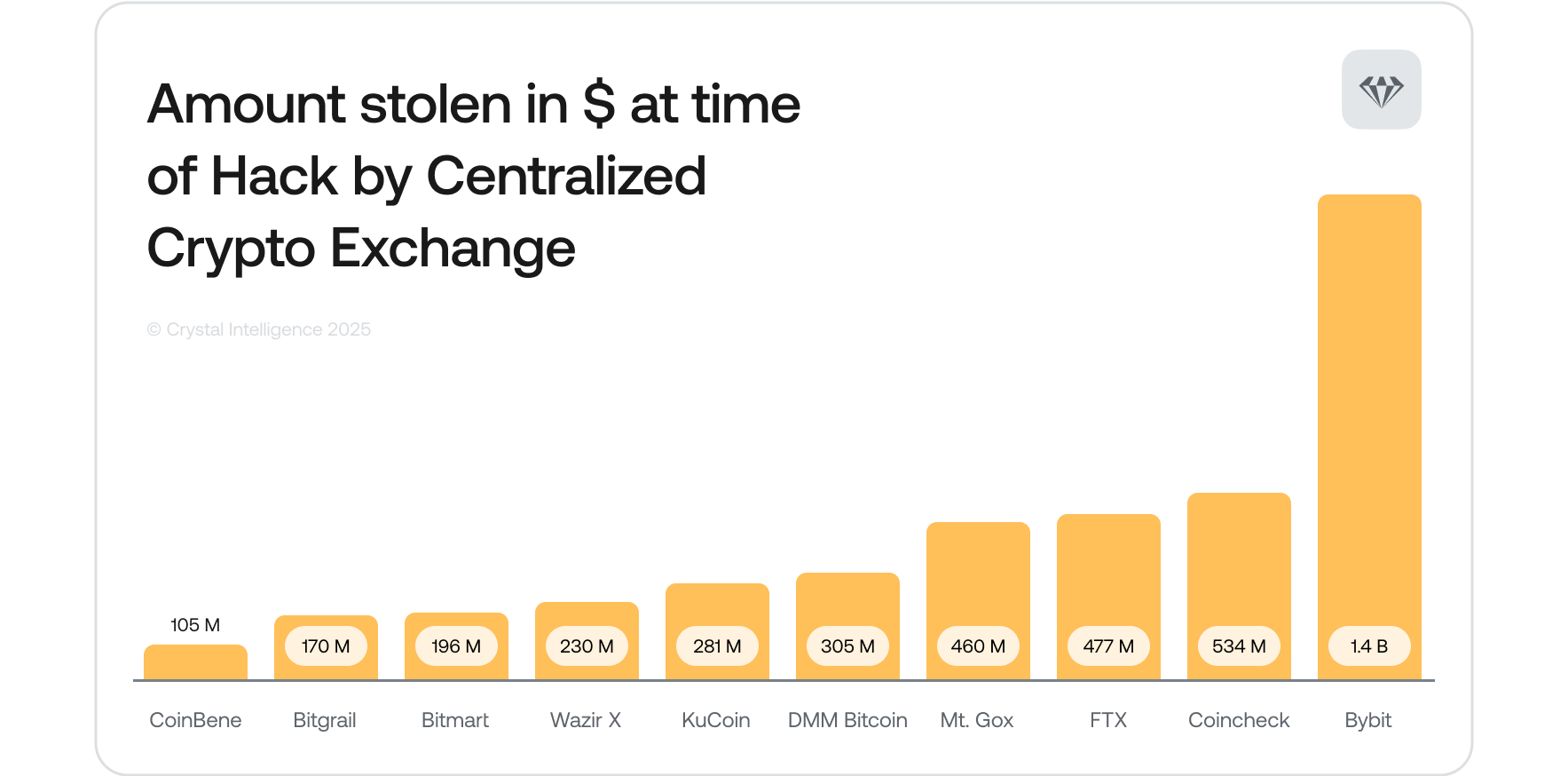
Then read this Exchange Hacks Greatest Hits autopsy, and take a look at this:
Source: CryptoIntelligence
And this:
Got it? Let’s move on.
Non-custodial hot wallets: everyday access with self-custody
Non-custodial hot wallets, the browser extensions and mobile apps like MetaMask, Phantom, and Trust Wallet, give you full control of your private keys while keeping the interface familiar and responsive.
They connect directly to DeFi protocols, decentralised exchanges, NFT marketplaces, and Web3 applications. For active Web3 users, they are essentially unavoidable. You cannot interact with most of the on-chain world without one.
The security picture is more nuanced than with custodial wallets. Because you control the keys, no exchange collapse can touch your funds. But the internet connection remains a live attack surface, and that means phishing, malicious transaction approvals, and front-end compromises are genuine and constant risks.
The approval problem
When you connect a hot wallet to a dApp and sign a transaction, you may be granting that contract permissions you did not fully read. A malicious approval can authorise a contract to drain specific tokens from your wallet, sometimes without any further interaction required on your part. The SetApprovalForAll exploit is one of the more aggressive versions of this, granting blanket permission to move an entire token category. Sign it once carelessly, and you’ve handed someone the keys to a specific slice of your holdings.
The phishing problem
Attackers build convincing copies of legitimate sites, or compromise the front-ends of real ones, and wait for users to connect. In Q2 2025, phishing accounted for roughly 49% of all crypto losses by value, making it the single largest attack vector for that period. That is not a niche threat. It is the primary way people lose funds.
This is where a browser-level security layer makes a real difference. Kerberus Sentinel3 monitors Web3 activity in real time, blocking known malicious sites before your wallet ever connects, and flagging suspicious transaction approvals before you sign them. It runs quietly in the background across 1,000+ EVM chains and Solana, and requires zero Web3 knowledge to use.
What non-custodial hot wallets are good for: Active trading, DeFi participation, regular dApp interaction, and anything requiring frequent on-chain transactions. Treat them like a spending account. Keep only what you need for active use.
What they are not good for: Storing the bulk of your holdings.
Hardware Wallets: Cold Cold Hard

A hardware wallet is a physical device, Ledger and Trezor are the most widely used, that keeps your private keys offline at all times. When you initiate a transaction, the signing happens inside the device itself. Only the signed transaction is broadcast to the network. The keys never touch your computer.
Even a completely malware-infected machine cannot extract your keys, because they never leave the device. This architecture makes hardware wallets the most widely recommended option for securing significant crypto holdings over the long term.
The practical trade-offs are worth naming honestly:
- Hardware wallets cost money (typically $70-$200 depending on the model).
- They require secure physical storage, which is its own problem to solve.
- Every transaction involves plugging in the device, navigating on-device menus, and confirming on a small screen.
For someone moving in and out of positions daily, that friction adds up fast. For a long-term HODLer who touches their holdings a handful of times a year, it is a feature rather than a bug.
The seed phrase is the real key
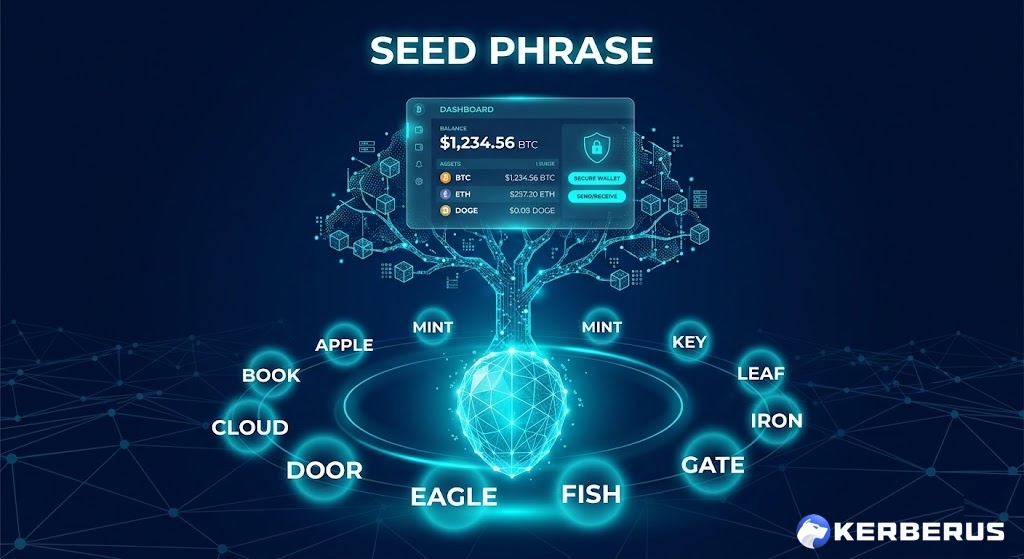
Every hardware wallet generates a recovery phrase during setup, typically 12 or 24 words, that can regenerate your keys on any compatible device. If your hardware wallet is lost, damaged, or destroyed, that phrase is how you recover everything.
Which also means: if someone else gets that phrase, whether through theft, a phishing attack, or a social engineering approach, they can empty your wallet from anywhere in the world. The device itself is irrelevant at that point.
So memorize the following (and not your seed phrase!)
- Write your seed phrase down.
- Store it offline.
- Never photograph it, never type it into any website.
- Never share it with anyone who asks, regardless of how legitimate they sound.
Read our guide on protecting your seed phrase if you want the full rundown on storage options.
Multisig wallets: safety through distribution
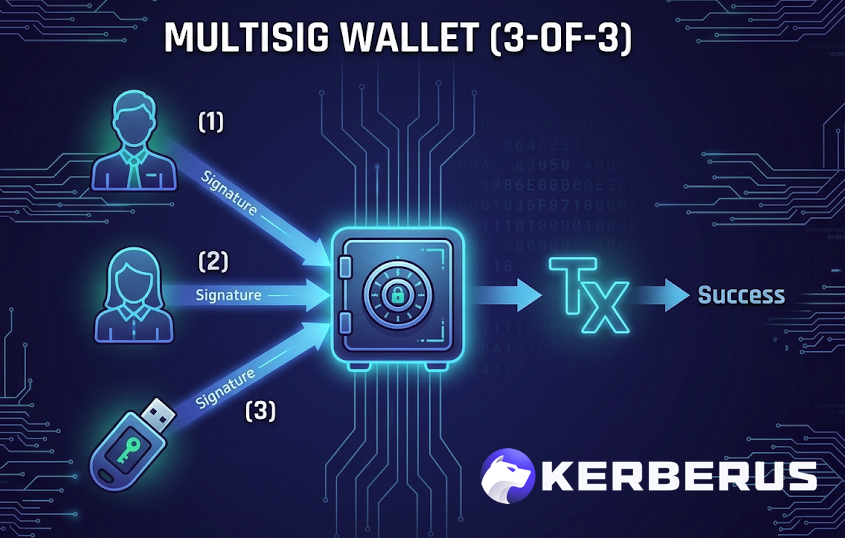
A multisig wallet requires multiple private key approvals before any transaction goes through. A 2-of-3 setup, for example, means that two out of three designated keys must sign before funds move. No single compromised key is enough to authorise a transfer.
This architecture is particularly valuable for organisations, DAOs, and high-net-worth individuals who want to distribute the risk of key compromise.
The Bybit incident in early 2025, in which attackers injected malicious code into the signing interface of a multisig wallet setup and caused staff to approve a transaction transferring $1.5 billion to attackers, proved emphatically that multisig is not invulnerable, but it does meaningfully raise the bar for attackers.
For individual users with substantial holdings, multisig adds a meaningful layer of protection at the cost of setup complexity.
Platforms like Safe (formerly Gnosis Safe) make the implementation more accessible than it once was.
Paper wallets: Offline but Fragile
A paper wallet is a printed or handwritten record of a public/private key pair, sometimes presented as a QR code. It is completely offline, costs nothing to create, and cannot be remotely hacked.
It can, however, be destroyed by fire or water, stolen, lost, or rendered illegible if the paper degrades. For most users, physical fragility is a bigger risk than it first appears. Paper wallets made more sense before hardware wallets became widely available. Today, they are rarely the right choice for anything beyond small amounts or novelty use.
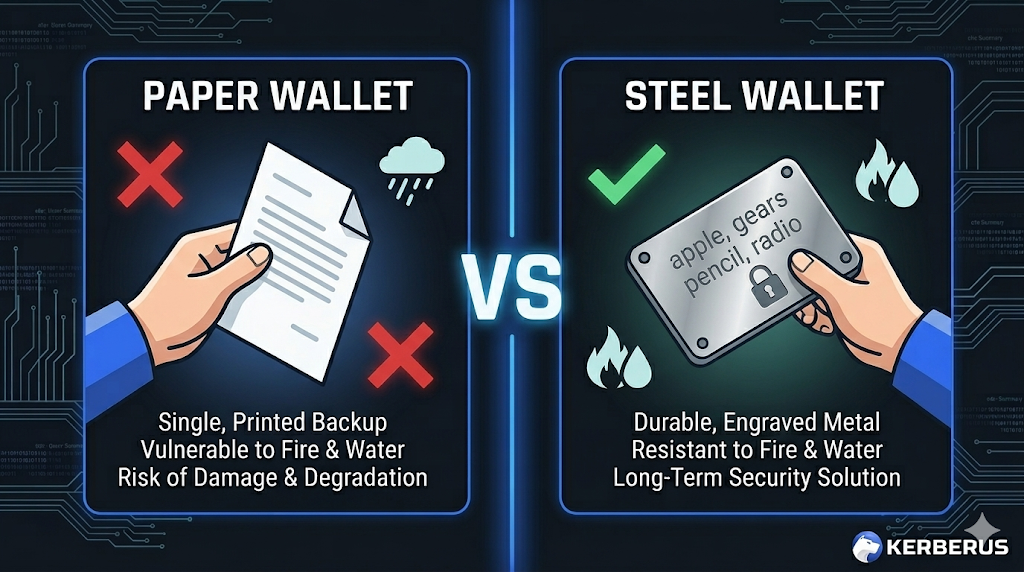
If you want a physically durable offline backup, steel wallets are a step up. They are fire-resistant, waterproof, and designed specifically for seed phrase storage. They are also expensive, and add one more physical item to secure.
How To Pick A Wallet Right For Your Crypto Usage
There is no universally correct answer when picking a crypto wallet. The right setup depends on your portfolio and what you’re actually doing with it.
If you are new to crypto and hold a small amount:
A custodial wallet on a reputable, regulated exchange is a reasonable starting point. Once you are comfortable with the basics, moving to self-custody makes sense.
If you actively trade or use DeFi:
A non-custodial hot wallet is necessary for the connectivity it provides. Keep only the amount you need for active use in that wallet. Treat it like a spending account, not a savings account.
If you hold significant amounts long-term:
A hardware wallet is the appropriate home for those assets. The friction is worth it. Keep your seed phrase offline and separate from the device.
If you do both: The most common approach among experienced users is a split setup. A hot wallet for active use, a hardware wallet for long-term holdings. The exact split depends on your risk tolerance, but a sensible default is to keep no more than you can afford to lose in any internet-connected wallet.
Kerberus: The security layer your wallet setup is missing
Picking the right wallet type is the foundation of your crypto security.
But wallet choice alone does not protect you from the threats that cause most losses in practice: phishing sites, malicious contract interactions, and social engineering attacks.
It can be all gone in one second.
Even hardware wallet users connect to the internet when initiating transactions, and that connection is where attackers operate.
A convincing phishing site or a front-end compromise can intercept that moment and substitute a malicious transaction for the one you intended to sign.
This is where a dedicated security layer adds meaningful protection.
Kerberus Sentinel3 operates as a browser extension that monitors Web3 activity in real time, blocking malicious sites before wallet connection and flagging suspicious transactions before you sign them. It covers 1,000+ EVM chains and Solana, requires no Web3 knowledge to operate, and has recorded zero user losses since January 2023. For transactions that do slip through its 99.9% detection rate, up to $30,000 in coverage is available through Kerberus’s Fairside partnership.
A hardware wallet secures your keys. Sentinel3 secures the moment you use them.
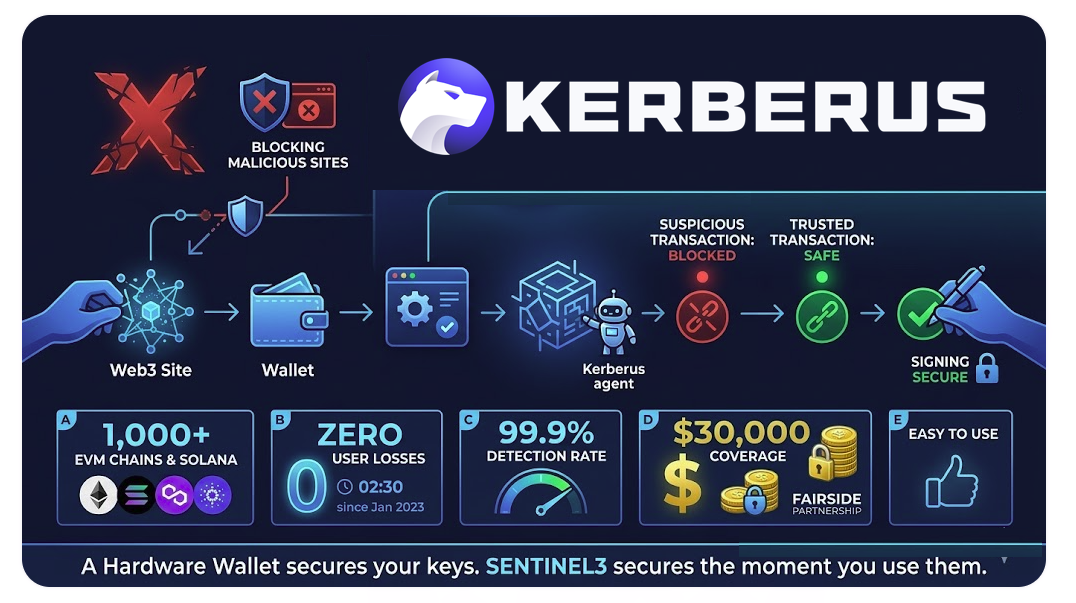
Kerberus Sentinel3 is built specifically for this gap. It operates as a browser extension that monitors Web3 activity in real time, blocking malicious sites before your wallet connects and flagging suspicious transaction approvals before you sign. It covers 1,000+ EVM chains and Solana, has recorded zero user losses since January 2023, and for transactions that do slip through its 99.9% detection rate, up to $30,000 in coverage is available through its Fairside partnership.
A hardware wallet secures your keys. Sentinel3 secures the moment you use them.
FAQ
What is the safest type of crypto wallet?
For long-term storage of significant holdings, a hardware wallet is the most secure option available to individual users. Your private keys never leave the device, which means remote attackers cannot extract them even from a malware-infected computer. That said, no hardware wallet protects you from yourself: a poorly stored seed phrase or a phishing attack that tricks you into entering your phrase somewhere online can still result in total loss.
What is the difference between a hot wallet and a cold wallet?
A hot wallet is connected to the internet, which makes it convenient for daily use but more exposed to remote attacks. A cold wallet keeps your private keys offline at all times. Hardware wallets are the most common type of cold wallet. The trade-off is transactional friction, which is intentional. More steps to sign a transaction means more opportunities for you to catch something wrong before it’s too late.
Is it safe to keep crypto on an exchange?
For small amounts you plan to trade actively, a reputable, regulated exchange is a reasonable option. For anything significant, it is not. Exchange collapses, regulatory freezes, sudden withdrawal restrictions, and direct hacks are real risks with extensive historical precedent. FTX wiped out billions in customer funds overnight. Cryptopia. Mt. Gox. Bitfinex. The list is long enough to take seriously.
What happens if I lose my hardware wallet?
Nothing, as long as you have your seed phrase stored safely. The seed phrase is a 12- or 24-word recovery phrase generated when you first set up the device. It can regenerate your keys on any compatible hardware wallet. This is also why the seed phrase itself needs to be treated with the same care as the funds it protects.
What is a non-custodial wallet?
A non-custodial wallet is one where you hold your own private keys rather than trusting a third party to hold them for you. Browser extensions like MetaMask and Phantom are common examples. You have full control over your assets, which also means full responsibility. There is no customer support to call if you lose access.
Do I need more than one wallet?
Most experienced crypto users run at least two: a hot wallet for active use and a hardware wallet for long-term storage. Think of it like a current account and a savings account. Keep what you need for daily activity accessible, and store everything else somewhere more secure. Layering a real-time security tool like Sentinel3 on top covers the threat surface that wallet choice alone cannot address.
About Kerberus

Kerberus is a Web3 security company founded by Danor Cohen, former Head of Offensive Security at Salesforce and a top-10 PayPal bug hunter, and Alex Katz, with a decade of global operations experience.
Their flagship product, Sentinel3, is a browser extension that provides real-time protection against wallet drainers, phishing attacks, malicious transaction approvals, and address poisoning across 1,000+ EVM chains and Solana. Sentinel3 has recorded zero user losses since January 2023, serves more than 250,000 users, and offers up to $30,000 in transaction coverage through a partnership with Fairside. The Kerberus enterprise API is available to wallets and platforms at zero cost.
Protect every transaction, not just your keys
The wallet setup covered here handles the storage problem. The attack surface that causes most real-world losses sits at the point of use, when you connect, approve, and sign. That is where Kerberus Sentinel3 operates.
Install Sentinel3 and run it alongside whatever wallet setup you choose. Cold storage secures your long-term holdings. Sentinel3 secures the moments in between.
Related reading:
Written by:
Werner Vermaak is a Web3 author and crypto journalist with a strong interest in cybersecurity, DeFi, and emerging blockchain infrastructure. With more than eight years of industry experience creating over 1000 educational articles for leading Web3 teams, he produces clear, accurate, and actionable organic material for crypto users.
- •8+ years in crypto & blockchain journalism
- •1000+ educational articles for leading Web3 teams
- •Former content lead at CoinMarketCap, Bybit, OKX
Related Guides
See more guides
Fake Airdrop Scams: Types and Red Flags To Avoid
Apr 10, 2026 • 4 minutes read

How to Revoke Crypto Token Approvals in 2026
Mar 28, 2026 • 4 minutes read

How to Read a Crypto Transaction Before You Sign It
Mar 23, 2026 • 4 minutes read
Bitcoin 101 For Beginners: BTC’s Past, Present and Future
Mar 19, 2026 • 4 minutes read
Install once & immediately get protected from scams, phishing and hacks. Zero losses for 250k+ users in 3 years. Now with up to $30,000 in coverage.
