Smart Contract
Learn what a smart contract is, how it self-executes on a blockchain, and why smart contract vulnerabilities are one of crypto's biggest security risks.
What is a Smart Contract?
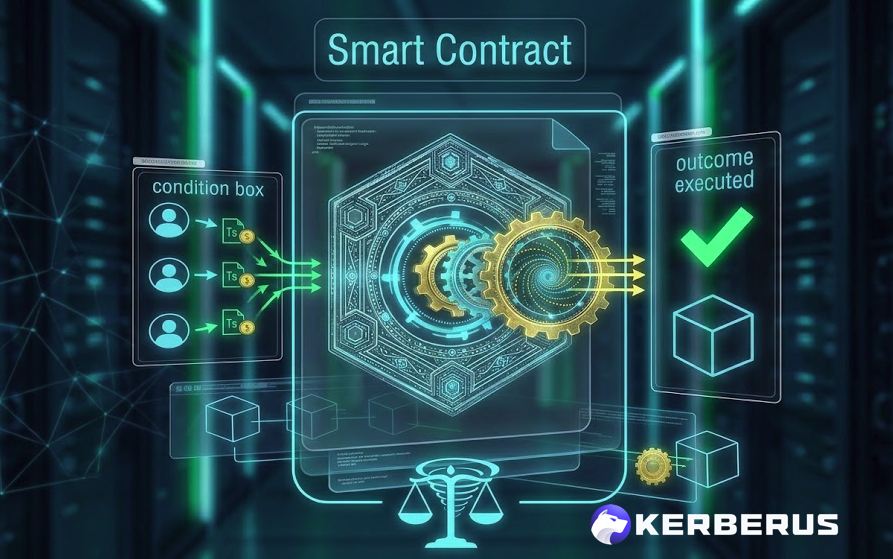
A smart contract is a self-executing program stored on a blockchain that automatically carries out a set of predefined instructions when specific conditions are met, with no human intermediary needed to enforce or trigger it. Write the rules into the code, deploy it to the blockchain, and it runs exactly as written, forever.
The term was coined by computer scientist Nick Szabo in the 1990s, long before blockchain made it practical. Ethereum, launched in 2015, became the first major platform to make smart contracts widely deployable, and they now form the backbone of DeFi, NFTs, token creation, and most of what makes Web3 different from the previous internet.
How It Works
Think of a smart contract like a vending machine. You insert the correct amount of money, press the button, and the machine releases your snack automatically. No cashier, no negotiation, no trust required.
A smart contract works the same way, except the “machine” is code running on thousands of computers simultaneously and the terms can be as complex as a full financial agreement.
Here’s a simple example: A decentralized exchange uses a smart contract to handle token swaps. When you send Token A to the contract, it automatically calculates how much Token B you should receive, sends it to your wallet, and records everything on the blockchain, all in a single transaction taking seconds.
The problem is that smart contracts are only as reliable as the code they’re written in. Bugs, design flaws, and overlooked edge cases can be exploited by attackers. The 2016 Ethereum DAO hack drained approximately $60 million through a reentrancy vulnerability, a flaw where a contract could be called repeatedly before it finished processing the first request. More recently, smart contract exploits across DeFi protocols cost users billions between 2021 and 2024.
How to Reduce Risk
-
Choose DeFi protocols whose smart contracts have been independently audited by reputable security firms, and check that the audit is recent and publicly available.
-
Avoid interacting with brand-new, unaudited contracts offering unusually high yields, as these are common setups for rugpulls and honeypot traps.
-
Review what permissions you’re granting when you sign a transaction. Some smart contracts request unlimited approval to spend your tokens.
-
Revoke outdated or unnecessary token approvals with tools like Revoke.cash.
-
Use the best Web3 security tools like Kerberus and Pocket Universe to get real-time protection and warnings when interacting with Web3 platforms
-
Check our Learn academy for top crypto safety information
Real-World Cases
In December 2025, Unleash Protocol lost approximately $3.9 million when an attacker exploited a governance flaw in its multisig smart contract, gaining administrative access and forcing an unauthorized contract update that enabled unrestricted fund withdrawals. SlowMist recorded 200 DeFi protocol hacks across 2025, totalling $2.9 billion in losses, a 40% increase on the year before.
FAQ
Q: What is a smart contract?
A: A smart contract is a self-executing program stored on a blockchain that automatically carries out predefined instructions when specific conditions are met. No human intermediary is needed to enforce or trigger it. Once deployed, it runs exactly as written. Smart contracts power DeFi protocols, NFTs, token creation, and most Web3 applications.
Q: How does a smart contract work?
A: Think of a smart contract like a vending machine: insert the right input and it automatically delivers the output. When you send tokens to a contract, it calculates what you should receive, executes the transfer, and records everything on the blockchain in seconds, with no company or person in between managing the process.
Q: How can users reduce the risk of smart contract exploits?
A: Use protocols whose contracts have been independently audited by reputable security firms, and verify the audit is recent and publicly available. Avoid unaudited contracts offering unusually high yields.
Always review the permissions a transaction requests before signing, and regularly revoke unnecessary token approvals using a tool like Revoke.cash.
Written by:
Werner Vermaak is a Web3 author and crypto journalist with a strong interest in cybersecurity, DeFi, and emerging blockchain infrastructure. With more than eight years of industry experience creating over 1000 educational articles for leading Web3 teams, he produces clear, accurate, and actionable organic material for crypto users.
- •8+ years in crypto & blockchain journalism
- •1000+ educational articles for leading Web3 teams
- •Former content lead at CoinMarketCap, Bybit, OKX
Related Terms
See more glossary termsInstall once & immediately get protected from scams, phishing and hacks. Zero losses for 250k+ users in 3 years. Now with up to $30,000 in coverage.