Layer 2
Learn what a Layer-2 network is, how rollups and state channels work, and what security risks exist when moving assets between Layer-1 and Layer-2 blockchains.

What is a Layer 2 chain?
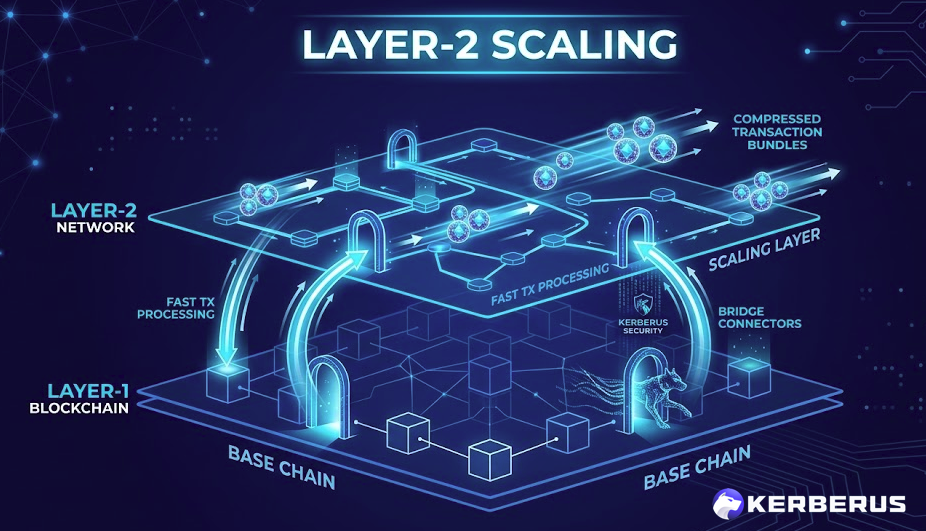
A Layer-2 (L2) network is a secondary protocol built on top of an existing Layer-1 blockchain that processes transactions off the main chain to increase speed and reduce costs, then posts compressed transaction data back to the L1 for final security.
Ethereum’s most widely used Layer-2 networks include Arbitrum, Optimism, Base, and zkSync. Together they handle billions of dollars in daily transaction volume while inheriting their ultimate security guarantees from Ethereum’s base layer.
Layer-2 networks make DeFi and Web3 usable for everyday transactions by bringing fees from several dollars down to fractions of a cent, without sacrificing the decentralization properties of the underlying chain.
How It Works
 In the first half of 2025, over $1.5 billion in stolen funds were funneled through cross-chain bridges, accounting for more than 50% of total theft, according to Global Ledger’s mid-2025 analysis.
In the first half of 2025, over $1.5 billion in stolen funds were funneled through cross-chain bridges, accounting for more than 50% of total theft, according to Global Ledger’s mid-2025 analysis.
The most popular Layer-2 architecture is the rollup. A rollup bundles hundreds or thousands of transactions together, processes them off-chain, and posts a compressed summary (plus a cryptographic proof) back to Ethereum.
There are two main types:
-
Optimistic rollups (like Arbitrum and Optimism) assume transactions are valid by default and allow a challenge window for fraud proofs of around 7 days.
-
ZK-rollups (like zkSync and StarkNet) use zero-knowledge cryptography to mathematically prove validity before posting to its L1.
The bridge is the critical link. To use a Layer-2, you move assets from a layer-1 chain like Ethereum through a bridge contract to the L2. When you’re done, you bridge back.
These bridge contracts hold enormous amounts of locked value and represent one of the most targeted attack surfaces in all of Web3.

In the first half of 2025, over $1.5 billion in stolen funds were funneled through cross-chain bridges, accounting for more than 50% of total theft, according to Global Ledger’s mid-2025 analysis.
In April 2025, ZKsync suffered a breach where an exploited admin wallet minted 111 million unclaimed ZK tokens worth $5 million from airdrop contracts, increasing circulating supply by 0.45%.
How to Reduce Risk
-
Only bridge assets through official, audited bridges maintained by the Layer-2 protocol itself, not third-party bridge aggregators with limited audit histories.
-
Avoid leaving large amounts locked in bridge contracts longer than necessary, withdraw to your main wallet once a transaction is complete.
-
Verify contract addresses before interacting with DeFi protocols on Layer-2 networks, as front-end compromises that redirect users to malicious contracts are increasingly common on L2s.
-
Use Kerberus Sentinel3 to screen dApp URLs on Layer-2 networks before connecting your wallet, stopping malicious sites before any transaction is signed.
FAQ
Q: What is a Layer-2 network?
A: A Layer-2 network is a secondary protocol built on top of a Layer-1 blockchain like Ethereum that processes transactions off-chain to increase speed and reduce costs. It then posts compressed transaction data back to the Layer-1 for final security. Examples include Arbitrum, Optimism, Base, and zkSync, all of which inherit security from Ethereum.
Q: How does a Layer-2 network work?
A: Most Layer-2 networks use rollups, which bundle hundreds of transactions together, process them off-chain, and post a compressed summary with a cryptographic proof back to Ethereum. Optimistic rollups assume transactions are valid and allow challenge windows for disputes. ZK-rollups mathematically prove validity before posting. Users move assets between L1 and L2 through bridge contracts.
Q: How can users reduce risk when using Layer-2 networks?
A: Only use official, audited bridges from the Layer-2 protocol itself. Avoid leaving assets locked in bridge contracts longer than necessary. Verify contract addresses before using DeFi protocols on L2 networks, as front-end compromises increasingly target these chains. Kerberus Sentinel3 can screen dApp URLs on Layer-2 networks before your wallet connects to them.
Written by:
Werner Vermaak is a Web3 author and crypto journalist with a strong interest in cybersecurity, DeFi, and emerging blockchain infrastructure. With more than eight years of industry experience creating over 1000 educational articles for leading Web3 teams, he produces clear, accurate, and actionable organic material for crypto users.
- •8+ years in crypto & blockchain journalism
- •1000+ educational articles for leading Web3 teams
- •Former content lead at CoinMarketCap, Bybit, OKX
Related Terms
See more glossary termsInstall once & immediately get protected from scams, phishing and hacks. Zero losses for 250k+ users in 3 years. Now with up to $30,000 in coverage.